Russian Spy Tied to DNC Hacking Arrested for Treason
Emrah Gurel
ByJOSH MARSHALL
PublishedJANUARY 25, 2017, 8:07 PM EDT
I had seen references to this over the last two days. But those references were in publications I was not familiar with or, so I was told, in Russian language publications which I couldn't read. But now The New York Times is reporting that the number two man in the department which purportedly oversaw the hacking campaign against the Democratic party in the United States, Sergei Mikhailov, has been arrested for treason.
Putin-era Russia is rather limited when it comes to the rule of law. It is not uncommon for those who fall from grace to find themselves targeted with prosecution. This was the method by which Putin brought the oligarchs to heel early in his reign. But treason is of course the most serious of charges.
From the Times ....
A senior official in the Russian cyberintelligence department that American officials say oversaw last year’s election hacking has been arrested in Moscow on charges of treason, a Russian newspaper reported Wednesday.
The arrest of Sergei Mikhailov, a senior officer of the Federal Security Service, or F.S.B., the main successor agency to the K.G.B., is a rare instance of turmoil in the country’s usually shadowy cybersecurity apparatus slipping into public view.
Mr. Mikhailov served in the F.S.B.’s Center for Information Security, the agency’s cyberintelligence branch, which has been implicated in the American election hacking. But it is not clear whether the arrest was related to those intrusions.
It may not be clear or known. But given the crisis touched off by the hacking campaign, US accusations about it and sanctions tied to it, it rather beggars credulity that they are not connected. Meanwhile, the AP reports that a cybersecurity expert at a firm which works closely with the FSB (the successor to the KGB) has also been arrested.
A manager in charge of investigating hacking attacks at Russia's biggest cybersecurity firm has been arrested, the company said Wednesday.
Kaspersky Lab on Wednesday confirmed reports in Russia's respected Kommersant newspaper that Ruslan Stoyanov, head of its computer incidents investigations unit, was arrested in December. Kommersant said that Stoyanov was arrested along with a senior Russian FSB intelligence officer and that they both face charges of treason.
These two arrests are being reported as coming right upon one another and presumably related. But a week and a half ago there was another development. Andrei Gerasimov, the head of the FSB’s Information Security Center since 2009 was fired. There was speculation in the press that the dismissal was corruption related. A reporter for Agence France-Presse speculated on twitter whether the dismissal might have been tied to the revelation of the Trump 'dossier' published by Buzzfeed.
Could this be an olive branch to Trump? Could this person have been accused of being an asset of US intelligence? Russian politics are notoriously opaque, their espionage and legal system even more so. Knowing very little about any of them, I have little basis to speculate. But someone fairly consequential seems to be up.
[ed.note: The original version of this post said that Mikhailov was the man US intelligence believes oversaw the hacking campaign against the Democratic party as opposed to the number two official in the FSB department which US intelligence believes oversaw the campaign. The original version was based on my misreading of the Times lede. I regret the error.]
http://talkingpointsmemo.com/edblog/rus ... or-treason
SECURITY PROS FEAR CHILLING EFFECT AS RUSSIA CHARGES INVESTIGATOR WITH TREASON
By Mark Coppock — January 25, 2017 6:18 PM
Our data privacy and security could be impacted by the political ramifications of information security investigations.
Safe computing requires the involvement of people in all industries, locations, and fields of expertise. Normally, that’s not a problem, as most people are willing and able to provide whatever input is necessary to help alleviate security risks in the technology we all use.
Some regions of the world are not as free and open as others, however, and so not all professionals as able to participate without concern for their own safety. Such could be the case with a Kaspersky Lab investigator who was arrested for treason in Russia, as Ars Technica reports.
Kaspersky Labs was quick to disassociate itself from the incident, saying, “The case against this employee does not involve Kaspersky Lab. The employee, who is Head of the Computer Incidents Investigation Team, is under investigation for a period predating his employment at Kaspersky Lab. We do not possess details of the investigation. The work of Kaspersky Lab’s Computer Incidents Investigation Team is unaffected by these developments.”
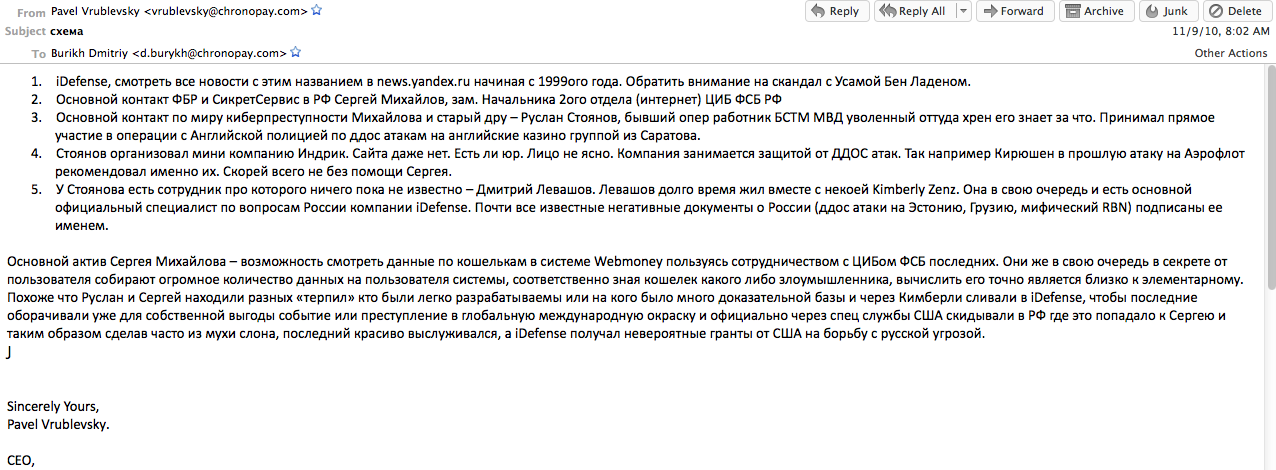
Details are sketchy as to why the investigator, Ruslan Stoyanov, was arrested. Stoyanov was in charge of Kaspersky Lab’s investigations unit, in addition to serving in Russia’s Ministry of Interior in charge of cybercrime. As Forbes reports, Stoyanov’s arrest might be related to an investigation involving Sergei Mikhailov, deputy head of the information security department of the FSB, involving monies paid by foreign companies.
However, Stoyanov recently contributed to the Kaspersky Lab Securelist blog, posting on cybercrime in Russia, and the Lawfare Blog has speculated — perhaps erroneously — that Stoyanov might have been a source of information leading to the conclusion that Russia sponsored hacking efforts aimed at interfering with the 2016 presidential election in the U.S. While nobody can be certain of the reasons for Stoyanov’s arrest, one general concern is that anyone who participates in efforts to fight cybercrime can come under political fire.
As Jake Williams of security firm Rendition Software put it, “For those living and working under oppressive regimes, keep up the good fight. But also remember that no incident response report or conference talk is worth jail time (or worse). I think that these charges will cause security researchers, particularly those in states with oppressive governments, to carefully consider the weight of reporting details of security incidents.”
Stoyanov’s arrest was filed under Article 275 of the Russian criminal code, which can impose treason charges on anyone who provides financial, technical, advisory, or other assistance to foreign states or organizations that are not friendly to Russia. This means that, as Forbes indicated in its coverage, merely providing the U.S. FBI with insights on malware such as botnets could run someone afoul of government agencies.
Nevertheless, the chilling effect on cybercrime research and mitigation could be significant if Stoyanov’s arrest indicates a trend of penalizing researchers and others for international cooperation. Even if Stoyanov’s arrest was for unrelated reasons, anyone involved with researching security in countries with oppressive governments might now think twice before working with foreign entities on resolving information security concerns.
http://www.digitaltrends.com/computing/ ... z4Wq0ZhRBy
Zero Hedge take
Head Of Investigations At Russia's Biggest Cybersecurity Firm Arrested For Treason
by Tyler Durden
Jan 25, 2017 12:13 PM
In what may be the latest fallout from the cold cyberwar taking place between the US and Russia, the head of the investigation unit, and one of the most important cybercrime experts at Kaspersky Lab, Russia's biggest cybersecurity firm, was been arrested on charges of treason. Stoyanov was involved in every big anti-cybercrime operation in Russia in past years, including the one against the components of the Lurk cybercrime gang.
Kaspersky Lab confirmed to AP reports in Russia's Kommersant newspaper that Ruslan Stoyanov, head of its computer incidents investigations unit, was arrested in December.
Ruslan Stoyanov
According to the “Kommersant” the arrest may be linked to the investigation on into Sergei Mikhailov, deputy head of the information security department of the FSB, Russia national security service. Stoyanov and Mikhailov were both arrested in December, according to the Kommersant the investigation was exploring the receipt of money from foreign companies by Stoyanov and his links to Mikhailov. Mikhailov is also facing treason charges alongside Stoyanov.
Kaspersky spokeswoman Maria Shirokova, said in a statement that Stoyanov's arrest "has nothing to do with Kaspersky Lab and its operations."
She said the company has no details of the charges Stoyanov faces, but added that the investigation dates back to the time before Stoyanov was hired by Kaspersky.
According to Forbes, the arrest may be a matter of national security: "A Russia-based information security source told FORBES the details of the case were likely to remain private. The case has been filed under article 275 of Russia’s criminal code, the source said, meaning it should result in a secret military tribunal. Article 275 allows the government to prosecute when an individual provides assistance to a foreign state or organization regarding “hostile activities to the detriment of the external security of the Russian Federation” (translation from source). According to the source, this can be applied broadly. For instance, furnishing the FBI with information on a botnet may amount to treason."
Before Stoyanov joined Kaspersky in 2012, he served six years as a major in the Ministry of Interior’s cybercrime unit between 2000 and 2006, then he moved into the private sector. While Ruslan Stoyanov was working for the Russian government, he was the lead investigator into a hacker crew that extorted $4 million to U.K. betting shops under the DDoS threat.
U.S. intelligence agencies have accused Russia of meddling in the U.S. presidential election through hacking, to help Donald Trump win the vote, claims that Russia has rejected. U.S. and EU officials also have accused Russia of hacking other Western institutions and voiced concern that Russia may try to influence this year's elections in Germany, France and the Netherlands. It wasn't immediately clear if the arrests are somehow linked to these allegations.
The FSB's press office did not comment on the arrest.
Meanwhile Andrei Soldatov, who has studied the internet and Russian security services for more than a decade, called the arrest of the Kaspersky manager "unprecedented."
"It destroys a system that has been 20 years in the making, the system of relations between intelligence agencies and companies like Kaspersky," he told The Associated Press. "Intelligence agencies used to ask for Kaspersky's advice, and this is how informal ties were built. This romance is clearly over."
While Kaspersky has published research damaging to Russian hacking operations, Eugene Kaspersky is known to have held a friendly relationship with the Russian government. The company has a strong international presence, including antivirus research facilities inside the United States.
It remains unclear if today's arrest has any connection to the "Russian election hacking" scandal that brought US-Russian relations to a halt in the last days of the Obama administration.
http://www.zerohedge.com/news/2017-01-2 ... ed-treason
Does Trump Have Ties To The Mob?
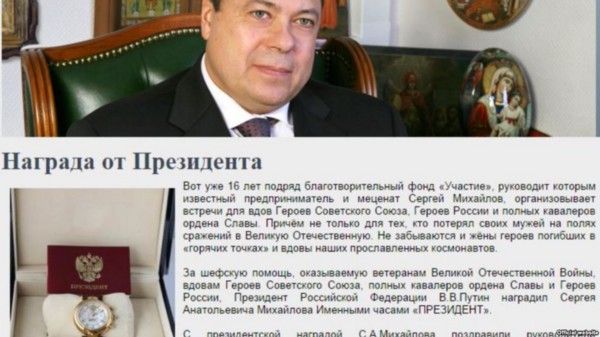
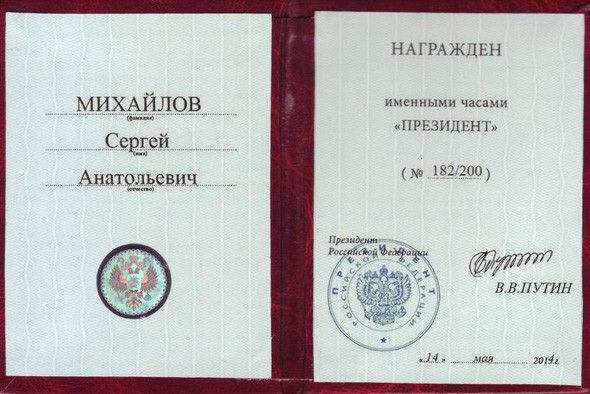
Alex Shnaider, Trump's partner for Trump Tower Toronto, has ties to Sergei Mikhailov, leader of the SoInsteva Gang, a ruthless "Russian crime syndicate."
http://www.dailywire.com/news/3936/does ... on-bandler
project went belly-up this November and has now entered foreclosure
The Case of the Trump Toronto Tower and Hotel—Alex Shnaider
Published on: December 19, 2016
RUSSIA & THE WEST
..........
Our fourth case study of Trump’s business associates concerns the 48-year-old Russian-Canadian billionaire Alex Shnaider, who co-financed the seventy-story Trump Tower and Hotel, Canada’s tallest building. It opened in Toronto in 2012. Unfortunately, like so many of Trump’s other Russia/FSU-financed projects, this massive Toronto condo-hotel project went belly-up this November and has now entered foreclosure.
According to an online profile of Shnaider by a Ukrainian news agency, Alex Shnaider was born in Leningrad in 1968, the son of “Евсей Шнайдер,” or “Evsei Shnaider” in Russian.30 A recent Forbes article says that he and his family emigrated to Israel from Russia when he was four and then relocated to Toronto when he was 13-14. The Ukrainian news agency says that Alex’s familly soon established “one of the most successful stories in Toronto’s Russian quarter, “ and that young Alex, with “an entrepreneurial streak,” “helped his father Evsei Shnaider in the business, placing goods on the shelves and wiping floors.”
Eventually that proved to be a great decision—Shnaider prospered in the New World. Much of this was no doubt due to raw talent. But it also appears that for a time he got significant helping hand from his (now reportedly ex-) father-in-law, another colorful Russian-Canadian, Boris J. Birshtein.
Originally from Lithuania, Birshtein, now about 69, has been a Canadian citizen since at least 1982.31 He resided in Zurich for a time in the early 1990s, but then returned to Toronto and New York.32 One of his key companies was called Seabeco SA, a “trading” company that was registered in Zurich in December 1982.33 By the early 1990s Birshtein and his partners had started many other Seabeco-related companies in a wide variety of locations, inclding Antwerp,34 Toronto,35 Winnipeg,36 Moscow, Delaware,37 Panama,38 and Zurich.39 Several of these are still active.40 He often staffed them with directors and officers from a far-flung network of Russians, emissaries from other FSU countries like Kyrgyzstan and Moldova, and recent Russia/FSU emigres to Canada.41
According to the Financial Times and the FBI, in addition to running Seabeco, Birshtein was a close business associate of Sergei Mikhaylov, the reputed head of Solntsevskaya Bratva, the Russian mob’s largest branch, and the world’s highest-grossing organized crime group as of 2014, according to Fortune.42 A 1996 FBI intelligence report cited by the FT claims that Birshtein hosted a meeting in his Tel Aviv office for Mikhaylov, the Ukrainian-born Semion Mogilevich, and several other leaders of the Russo/FSU mafia, in order to discuss “sharing interests in Ukraine.”43 A subsequent 1998 FBI Intelligence report on the “Semion Mogilevich Organization” repeated the same charge,44 and described Mogilevich’s successful attempts at gaining control over Ukraine privatization assets. The FT article also described how Birshtein and his associates had acquired extraordinary influence with key Ukraine officials, including President Leonid Kuchma, with the help of up to $5 million of payoffs.45 Citing Swiss and Belgian investigators, the FT also claimed that Birshtein and Mikhaylov jointly controlled a Belgian company called MAB International in the early 1990s.46 During that period, those same investigators reportedly observed transfers worth millions of dollars between accounts held by Mikhaylov, Birshtein, and Alexander Volkov, Seabeco’s representative in Ukraine.
In 1993, the Yeltsin government reportedly accused Birshtein of illegally exporting seven million tons of Russian oil and laundering the proceeds.47 Dmytro Iakoubovski, a former associate of Birshtein’s who had also moved to Toronto, was said to be cooperating with the Russian investigation. One night a gunman fired three shots into Iakoubovski’s home, leaving a note warning him to cease his cooperation, according to a New York Times article published that year. As noted above, according to the Belgian newspaper Le Soir, two members of Bayrock’s Eurasian Trio were also involved in Seabeco during this period as well—Patokh Chodiev and Alexander Mashkevich. Chodiev reportedly first met Birshtein through the Soviet Foreign Ministry, and then went on to run Seabeco’s Moscow office before joining its Belgium office in 1991. Le Soir further claims that Mashkevich worked for Seabeco too, and that this was actually how he and Chodiev had first met.
All this is fascinating, but what about the connections between Birshtein and Trump’s Toronto business associate, Alex Shnaider? Again, the leads we have are tantalizing.The Toronto Globe and Mail reported that in 1991, while enrolled in law school, young Alex Shnaider started working for Birshtein at Seabeco’s Zurich headquarters, where he was reportedly introduced to steel trading. Evidently this was much more than just a job; the Zurich company registry lists “Alex Shnaider” as a director of “Seabeco Metals AG” from March 1993 to January 1994.48
In 1994, according to this account, he reportedly left Seabeco in January 1994 to start his own trading company in Antwerp, in partnership with a Belgian trader-partner. Curiously, Le Soir also says that Mikhaylov and Birshtein co-founded MAB International in Antwerp in January 1994. Is it far-fetched to suspect that Alex Shnaider and mob boss Mikhaylov might have crossed paths, since they were both in the same city and they were both close to Shnaider’s father-in-law?
According to Forbes, soon after Shnaider moved to Antwerp, he started visiting the factories of his steel trading partners in Ukraine.49 His favorite client was the Zaporizhstal steel mill, Ukraine’s fourth largest. At the Zaporizhstal mill he reportedly met Eduard Shifrin (aka Shyfrin), a metals trader with a doctorate in metallurgical engineering. Together they founded Midland Resource Holdings Ltd. in 1994.50
As the Forbes piece argues, with privatization sweeping Eastern Europe, private investors were jockeying to buy up the government’s shares in Zaprozhstal. But most traders lacked the financial backing and political connectons to accumulate large risky positions. Shnaider and Shifrin, in contrast, started buying up shares without limit, as if their pockets and connections were very deep. By 2001 they had purchased 93 percent of the plant for about $70 million, a stake that would be worth much more just five years later, when Shnaider reportedly turned down a $1.2 billion offer.
Today, Midland Resources Holdings Ltd. reportedly generates more than $4 billion a year of revenue and has numerous subsidiaries all across Eastern Europe.51 Shnaider also reportedly owns Talon International Development, the firm that oversaw construction of the Trump hotel-tower in Toronto. All this wealth apparently helped Iceland’s FL Group decide that it could afford to extend a €45.8 million loan to Alex Shnaider in 2008 to buy a yacht.52
As of December 2016, a search of the Panama Papers database found no fewer than 28 offshore companies that have been associated with “Midland Resources Holding Limited.”53 According to the database, “Midland Resources Holding Limited” was a shareholder in at least two of these companies, alongside an individual named “Oleg Sheykhametov.”54 The two companies, Olave Equities Limited and Colley International Marketing SA, were both registered and active in the British Virgin Islands from 2007–10.55 A Russian restaurateur by that same name reportedly runs a business owned by two other alleged Solntsevskaya mob associates, Lev Kvetnoy and Andrei Skoch, both of whom appear with Sergei Mikhaylov. Of course mere inclusion in such a group photo is not evidence of wrongdoing. (See the photo here.) According to Forbes, Kvetnoy is the 55th richest person in Russia and Skoch, now a deputy in the Russian Duma, is the 18th.56
Finally, it is also intriguing to note that Boris Birshtein is also listed as the President of “ME Moldova Enterprises AG,” a Zurich-based company” that was founded in November 1992, transferred to the canton of Schwyz in September 1994, and liquidated and cancelled in January 1999.57 Birshstein was a member of the company’s board of directors from November 1992 to January 1994, when he became its President. At that point he was succeeded as President in June 1994 by one “Evsei Shnaider, Canadian citizen, resident in Zurich,” who was also listed as director of the company in September 1994.58 “Evsei Schnaider” is also listed in the Panama registry as a Treasurer and Director of “The Seabeco Group Inc.,” formed on December 6, 1991,59 and as treasurer and director of Seabeco Security International Inc.,” formed on December 10, 1991. As of December 2016, both companies are still in existence.60 Boris Birshtein is listed as president and director of both companies.61
The Case of Paul Manafort’s Ukrainian Oligarchs
.........
http://www.the-american-interest.com/20 ... nnections/
Top Russian spy official arrested on treason charges
ANDREW E. KRAMER
The New York Times News Service
Published Wednesday, Jan. 25, 2017 6:23PM EST
Last updated Wednesday, Jan. 25, 2017 6:25PM EST
A senior official in the Russian cyberintelligence department that U.S. officials say oversaw last year’s election hacking has been arrested in Moscow on charges of treason, a Russian newspaper reported Wednesday.
The arrest of Sergei Mikhailov, a senior officer of the Federal Security Service (FSB), the main successor agency to the KGB, is a rare instance of turmoil in the country’s usually shadowy cybersecurity apparatus slipping into public view.
Mr. Mikhailov served in the FSB’s Centre for Information Security, the agency’s cyberintelligence branch, which has been implicated in the U.S. election hacking. But it is not clear whether the arrest was related to those intrusions.
He was detained along with one of Russia’s leading private-sector cybersecurity experts, Ruslan Stoyanov, the head of computer incident response investigations at the Kaspersky Lab, which makes anti-virus programs.
The company confirmed in a statement that Mr. Stoyanov had been arrested, but said his arrest “has nothing to do with Kaspersky Lab and its operations.”
Still, the arrests of the men, who had co-operated in Russia to prosecute cybercriminals, shed light on the sensitive intersection of cybercrime, private anti-virus companies and the Russian security services.
Western cybersecurity analysts have said there are indications that the security services recruited among criminal hackers to carry out politicized computer intrusions ahead of last summer’s hacking of the Democratic National Committee in the United States, giving the hackers impunity to commit financially motivated attacks in exchange for their expertise.
The arrest raised the possibility that Mr. Mikhailov and Mr. Stoyanov had interfered in this co-operation. The newspaper article, in Kommersant, which cited unnamed sources in Moscow’s technology industry and the FSB, said the treason charges related to work on criminal hacking investigations.
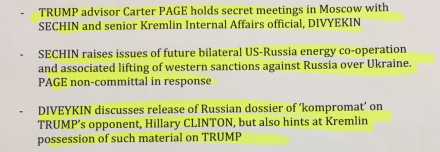
Alternatively, the detention of an official who would have been in a position to engage in the election hacking in America could indicate a goodwill gesture to the United States, which has sanctioned Russia for the electoral meddling.
U.S. intelligence agencies accused the FSB and another Russian agency, the military’s Main Intelligence Directorate (GRU), of hacking the Democratic National Committee and other electoral targets.
The sanctions targeted the two Russian intelligence agencies. But private U.S. cybersecurity investigators say the FSB, where Mr. Mikhailov was the second-most senior figure in the Centre for Information Security, operated a group nicknamed Cozy Bear that stole data but never released it. The GRU, the U.S. cybersleuths say, operated a group called Fancy Bear that stole electronic data and released it in an effort to help Donald Trump win the presidential election.
If confirmed, the arrest would be one of the highest-profile detentions for treason within the FSB since the breakup of the Soviet Union.
In another indication of high-level turmoil over cyberintelligence issues within the security agency, Kommersant reported on Jan. 13 that the director of the Centre for Information Security, Andrei Gerasimov, would be fired. His termination was related to the investigation into the agency’s co-operation with Kaspersky on criminal hacking cases.
Gerasimov, who has led the Centre for Information Security since 2009, was described as building close ties with companies like the Kaspersky Lab as an element in Russia’s cybersecurity policy. He is also the deputy director for counterintelligence at the FSB.
The FSB did not respond to an email query about the arrests.
http://www.theglobeandmail.com/news/wor ... e33766836/