Given the numerous references to the Guccifer 2.0 narratives across several related threads, I've set up this OP as a central repository for Guccifer-related news items/findings.
There's essentially 2 (conflicting) items of note:
1) According to analysis conducted by Crowdstrike, Guccifer is a likely (or confirmed, depending on news source) Russian agent. This is the primary narrative presented by various newsfeeds (Buzzfeed et al.)
2) Guccifer's motivations/nation of allegiance can NOT be confirmed; recent metadata analysis identify the West Coast, USA as a likely source location for document modifications.
Prior content within RI pertaining to Guccifer can be found on page 36 of the following thread, though there are other references across several other OPs as well:
viewtopic.php?f=8&t=29320&hilit=guccifer&start=525
I'll repeat a disclaimer I included in that thread:
Belligerent Savant » Fri Apr 06, 2018 7:46 pm wrote:.
...None of this can be confirmed/corroborated without access to the original source data, or the pristine forensic images that Crowdstrike claims to have obtained/analyzed.
EDITED TO ADD: my position remains: there is NO evidence confirming Guccifer's "source location", certainly not to the extent conveyed/suggested by most media outlets. Any media source identifying Guccifer as Russian -- without a caveat that his/her origin remains unsubstantiated -- is either lazy or suspect.
(Note to self: dispense with the inclination towards grandstanding/over-emphasis when attempting to illustrate a point.)
From that same thread, the following cross-post (x2) provides useful context as a primer:
Belligerent Savant » Sun Mar 25, 2018 11:33 am wrote:.
https://medium.com/homefront-rising/dum ... fa522ff44f
Excerpt:
“If I give you a malware binary to reverse engineer, what do you see?” This is the question that had been posited by Michael Tanji, the retired cyber intelligence analyst. “Exactly what the author wants you to see.”
I want you to see words in a language that would throw suspicion on someone else.
An article published in ArsTechnica highlighted the work of an independent security researcher, Adam Carter, who had uncovered evidence that some of the documents released by Guccifer 2.0 in his initial document dump had been manipulated in a manner which introduced Russian words, in the Cyrillic alphabet, into the metadata of the documents, including a reference to “Felix Edmundovich,” the first name and patronymic of the founder of the Soviet security service, Felix Dzerzhinsky. The combination of the Cyrillic alphabet and the reference to a Russian spymaster seems ideal if one is trying to attribute its existence to the Russian intelligence services.
I want you to see that my code was compiled in a particular foreign language (even though I only read and/or write in a totally different language).
FireEye, a well-known cyber security company, has written a report on APT-28 (another name for Fancy Bear), highlights a number of Russian language indicators, including the consistent use of Russian language in malware code over the course of six years.
I want you to see certain comments or coding styles that are the same or similar to someone else’s (because I reuse other people’s code.)
Fidelis Security, another well-known cyber security company, was provided samples of the Cozy Bear and Fancy Bear malware for “independent analysis.” According to Fidelis, these samples matched the description provided by CrowdStrike and “contained complex coding structures and utilized obfuscation techniques that we have seen advanced adversaries utilize in other investigations we have conducted,” Michael Buratowski, the senior vice president of security consulting services at Fidelis, noted. The malware was “at times identical to” malware that other cyber security vendors, such as Palo Alto Networks, have attributed to Fancy Bear. Many of these similarities have been previously identified by other cyber security vendors and made public as far back as 2013.
I want you to see data about compilation date/time, PDB file path, etc., which could lead you to draw erroneous conclusions have no bearing on malware behavior or capability.
FireEye, in its report on APT-28 (i.e., Fancy Bear), also notes that the compile times associated with the malware align with the work hours and holiday schedules of someone residing in the same time zone as Moscow and St. Petersburg.
The fascinating thing about Michael Tanji’s observations was that they were made in 2012, largely in response to the spate of China attributions headed up by Dmitri Alperovitch’s highly publicized 2011 Shady Rat report. Four years later, the fixation on pattern-derived attribution remained a problem within the cyber security collective, this time with Russia as the target de jour. In 2011, the Chinese caseload was spread across a broad field of separate cyber attacks. In 2016, the Russian data set was limited to a single event — the DNC cyber attack.
Moreover, the data set in 2016 was under the exclusive control of a single entity — CrowdStrike. While select malware samples were farmed out to like-minded vendors, for the most part outside analysis of the DNC cyber penetration was limited to the information provided by CrowdStrike in its initial report. Even the FBI found itself in the awkward position of being denied direct access to the DNC servers, having instead to make use of “forensic images” of the server provided by CrowdStrike, along with its investigative report and findings.
There is much unknown about these scans — were they taken from May 6, when CrowdStrike first detected what it assessed to be a Russian presence inside the DNC server? Or are they from June 10, the last day the server was in operation? The difference could be significant, keeping in mind the fact that there were more than 30 days between the two events.
In this intervening time, CrowdStrike watched Guccifer 2.0 exfiltrate documents. It also possibly engaged in offensive measures, such as the dangling of so-called “attractive data” (the Russian-language tainted opposition research documents come to mind.) The possibility of additional manipulation of data cannot be discounted. However, even though members of Congress are starting to call for the FBI to take physical possession of the server and conduct its own independent forensic investigation, the server remains in the possession of the DNC.
Through the release of its “Bears in the Midst” report, CrowdStrike anticipated that the US government and, by extension, the American people, would place their trust in CrowdStrike’s integrity regarding Russian attribution. The media has, for the most part, accepted at face value CrowdStrike’s Russian attribution regarding the DNC cyber attack.
The US government, while slower to come onboard, eventually published a Joint Statement by the Office of Director of National Intelligence and the Department of Homeland Security in October 2016 that declared, “The recent disclosures of alleged hacked e-mails…by the Guccifer 2.0 online persona are consistent with the methods and motivations of Russian-directed efforts.”
On December 29, 2016, the FBI and DHS released a Joint Analysis Report (JAR) that directly attributed the presence of both the Cozy Bear and Fancy Bear actors on the DNC server to “spearfishing” attacks, thereby eliminating from consideration any possibility that Guccifer 2.0 penetrated the DNC server through a “zero day” exploit. This was a curious assessment, given that the only data in existence regarding what had transpired inside the DNC server was the data collected by CrowdStrike — data CrowdStrike maintains did not provide evidence pertaining to how the DNC server was initially breached by either Cozy Bear or Fancy Bear.
The Director of National Intelligence followed up with a National Intelligence Assessment, released on January 6, 2017, that similarly endorsed the findings of CrowdStrike when it came to Russian attribution for the Cozy Bear and Fancy Bear penetration of the DNC, as well as linking Guccifer 2.0 to the GRU, or Russian military intelligence. It was the strength of this national assessment that closed the book on debate on the matter of Russian attribution. Senators and Congressmen, intelligence officials and media pundits — all seem to be in agreement that Russia was singularly responsible for the cyber attack against the DNC, and the subsequent release of documents acquired from that breach. “Without a doubt,” “undeniable,” “incontrovertible” — this was the verbiage that accompanied any discussion of the case against Russia.
The genesis moment for this collective clarity, however, remains the carefully choreographed release of the CrowdStrike report, “Bears in the Midst,” and the accompanying Washington Post exclusive laying the blame for the DNC cyber attack squarely at the feet of Russia. From this act all else followed, leading to the certainty that accompanied this attribution was enough to overcome the challenge posed by the sudden appearance of Guccifer 2.0, enabling the same sort of shoehorned analysis to occur that turned Guccifer 2.0 into a Russian agent as well.
Much of this discussion turns on the level of credibility given to the analysis used by CrowdStrike to underpin its conclusions. Alperovitch, the author of the “Bears in the Midst” report, does not have a good record in this regard; one need only look at the controversy surrounding the report he wrote on Shady Rat while working for McAfee. A new report released by Alperovitch and CrowdStrike casts further aspersions on Alperovitch’s prowess as a cyber analyst, and CrowdStrike’s overall methodology used to make its Russian attribution.
On December 22, 2016, CrowdStrike published a new report purporting to detail a new cyber intrusion by the Fancy Bear actor, titled “Danger Close: Fancy Bear Tracking of Ukrainian Field Artillery Units.” This analysis, prepared by Adam Meyers, CrowdStrike’s vice president for intelligence, was claimed to further support “CrowdStrike’s previous assessments that Fancy Bear is likely affiliated with the Russian military intelligence (GRU). This report was used to promote a Jan. 4 live discussion event with Meyers and Alperovitch, titled “Bear Hunting: History and Attribution of Russian Intelligence Operations,” which was intended to educate the audience on the links between Fancy Bear and the GRU.
The “Danger Close” report was presented as further validation of CrowdStrike’s Falcon Program, which CrowdStrike claims helps organizations stop cyber penetrations through proactive measures developed through a deep understanding of the adversary and the measures needed to stop them. It was Falcon that “lit up” ten seconds after being installed on the DNC server back on May 6, 2016, fingering Cozy Bear and Fancy Bear as the culprits in the DNC attack. Falcon was now being linked to this newest effort at Russian attribution.
The only problem for Meyers, Alperovitch and CrowdStrike was that “Danger Close” was wrong — dead wrong — in every aspect of its analysis. The report was dissected by none other than Jeffrey Carr — the same individual who criticized Alperovitch over his Shady Rat claims. One of Carr’s most important findings deals directly with the credibility methodology used by CrowdStrike to attribute Fancy Bear to the GRU. “Part of the evidence supporting Russian government involvement in the DNC and related hacks (including the German Bundestag and France’s TV5 Monde),” Carr writes, “stemmed from the assumption that X-Agent malware was exclusively developed and used by Fancy Bear. We now know that’s false, and that the source code has been obtained by others outside of Russia.” Carr cites at least two examples, one a security company, the other a hacker collective, of the X-Agent malware existing “in the wild.” If these two entities have the X-Agent malware, Carr notes, “then so do others, and attribution to APT28/Fancy Bear/GRU based solely upon the presumption of ‘exclusive use’ must be thrown out.”
In one fell swoop, Carr destroyed the very premise upon which CrowdStrike not only attributed the DNC cyber attack to Russia, but the heart and soul of CrowdStrike’s business platform — the Falcon Platform used by CrowdStrike to provide “end point” protection to its clients. Far from representing an intelligent platform capable of discerning threats through advanced algorithms and proprietary techniques, the Falcon Platform seems to be little more than a database pre-programmed to deliver a preordained finding — X-Agent equals Fancy Bear, and Fancy Bear equals Russia.
Also, metadata analysis by an independent researcher which contradicts the 'Russia Hack' narrative:
https://theforensicator.wordpress.com
Forensicator maintains his position that the most probable and plausible interpretation of the observations derived from the NGP VAN 7zip metadata is:
There is evidence that suggests the files in the NGP VAN archive were copied (twice) locally, on the East Coast, US. Further, there are indications that a USB-2 capable media may have been used for the first copy operation on July 5, 2016 and that a FAT-formatted media was used in the second copy operation on Sept. 1, 2016. (A USB flash drive is one of the most popular FAT-formatted media, but there are others including SD cards and removable hard drives.)
Essentially: files eventually published by the Guccifer 2.0 persona were likely initially downloaded by a person with physical access to a computer possibly connected to the internal DNC network. The individual most likely used a USB drive to copy the information.
The author of the (above-referenced) forensicator blog recently submitted updated analysis/findings, which I'll share below (LiminalO provided a link referencing these findings in the Russian Conspiracy as RI subject thread):
https://theforensicator.wordpress.com/g ... ngerprint/
Guccifer 2’s West Coast Fingerprint
Introduction
In this report, we analyze the time zone offset that was likely in force when Guccifer 2’s first five (5) Word documents were written. We also look at the time of day pattern of the “last modified” times for the 25/so documents that Guccifer 2 modified and then uploaded to his blog site.
Finally, we look at one particular Word document that Guccifer 2 uploaded, which had “track changes” enabled. From the tracking metadata we deduce the time zone offset in effect when Guccifer 2 made that change — we reach a surprising conclusion: The document was likely saved by Guccifer 2 on the West Coast, US.
Summary
- Using a technique recently disclosed by another researcher (David Blake), we were able to establish GMT time zone offsets for Guccifer 2’s first five (5) Word documents. Four of those documents (1.doc, 2.doc, 3.doc, and 5.doc) were created with GMT+3 time zone settings in effect. (During the summer of 2016, GMT+3 would have applied to Central Europe, the Middle East, and Western Russia.) One document, 4.doc, was created with GMT+4 time zone settings in force.
- We deduce that 4.doc‘s GMT+4 time setting indicates that Russian time zone settings were in force when that document was saved. This conclusion derives from the possible use of an outdated cracked Windows XP OS which did not receive updates to its time zone tables. Hypothetically, this unpatched OS was not updated to reflect the fact that Moscow/Russia dropped Daylight Saving Time for Western Russia in 2014. This conclusion also depends upon the user not adjusting their time zone offset manually for over three months after the time zone should have been corrected.
- Given that the user did not manually disable the DST time adjustment, we suggest that 4.doc may have been created on a VM that was purpose-built to “telegraph” the use of Russian time zone settings.
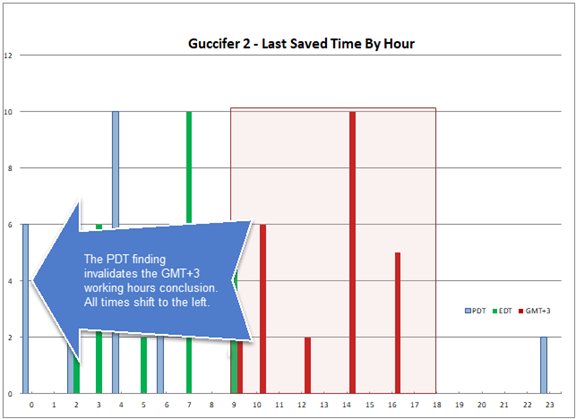
- We construct a histogram of the time of day that Guccifer 2 last modified the 25/so documents that he changed mainly for the purposes of manipulating their metadata (such as “last saved by” user, company name, etc). This histogram supports the conclusion that Guccifer 2 operated out of a region with a GMT+3 time zone offset in force.
- We analyze the timestamp on an internal “track changes” entry created by Guccifer 2 when he modified a document that was published in his second batch of documents that were uploaded to his WordPress site. We correlate this timestamp to the document’s “modified” (“last saved”) time recorded in the document’s metadata. Based on this analysis, we reach the surprising conclusion that this document was created on a system which had Pacific Daylight Saving Time (PDT) settings in force, when the change was made.
- The PDT finding draws into question the premise that Guccifer 2 was operating out of Russia, or any other region that would have had GMT+3 time zone offsets in force. Essentially, the Pacific Time Zone finding invalidates the GMT+3 time zone findings previously described.
Timeline
The following timeline summarizes some key events and developments as they relate to the analysis of Guccifer 2’s early document disclosures. For a much more detailed timeline, consult Adam Carter’s Guccifer 2 timeline.
[2013-07-13] As noted by Thomas Rid (@RidT), the original Guccifer (Marcel Lazăr Lehel) disclosed a similar version of Guccifer 2’s 4.doc in the summer of 2013. Additional metadata analysis indicates that the source document dates back to the time of the Obama administration (2008).
[2016-06-14] Via the Washington Post [archive] the DNC announced it has been hacked. The WaPo article mentions (in its headline and in the body of the article) that they fear that a Trump opposition research document (now known as 1.doc from Guccifer 2) may have been stolen by Russian state-sponsored operatives.
[2016-06-15] The security firm, Crowdstrike, who was hired by the DNC, published a blog [archive] which attributed the alleged DNC hack to Russian state actors.
[2016-06-15] Guccifer 2 arrived on the scene that same day. Guccifer 2 quickly published ten (10) Office documents on his WordPress.com blog [archive]. Five (5) of those are Word documents; they are analyzed in our companion report, Did Guccifer 2 Plant his Russian Fingerprints?. Guccifer 2 initially posed as a Romanian (lone wolf) hacker, but as time went on his story began to deteriorate. Some pundits quickly assigned Russian attribution to Guccifer 2, partly due to Cyrillic artifacts in his first five Word documents. Also, in an online chat, it was observed that Guccifer 2 had weak fluency in Romanian.
[2016-06-15] That same day, two media outlets published stories, covering 1.doc (the DNC sourced “Trump opposition report”), which was apparently pre-disclosed to them by Guccifer 2. Those media outlets were The Smoking Gun [archive] (TSG) and Gawker [archive].
[2016-06-15] Matt Tait (@pwnallthings), a security blogger/journalist, began following Guccifer 2. Matt started a Twitter mega-thread here. Matt’s involvement with Guccifer 2 will cause him to be interviewed by Mueller as part of the Mueller investigation of Michael Flynn [archive] in October, 2017.
[2016-06-16] One day later, a well known online media outlet, Ars Technica [archive], (which covers technology topics) reviewed the PDF [archive] posted by Gawker; this PDF is derived from 1.doc. Ars Technica noticed the presence of error messages located in the last few pages of the 200+ page PDF. Those messages were written in Russian (using the Cyrillic alphabet).
[2016-06-18] Guccifer 2 published his second batch of documents. One document from that batch had “track changes” enabled in Word; we focus on that document in this report.
[2016-06-18] In a tweet [archive], Tait noticed a document with “track changes” that Guccifer 2 had uploaded that same day. He reported on a small change that was made under the name “Ernesto Che”. His observation prompted us to analyze the date/time that this change was made. Based on our analysis, we conclude that this document was likely last modified by Guccifer 2 on the West Coast, US.
[2016-10-07] Wikileaks released their first batch of Podesta emails. Per our analysis, all five of Guccifer 2’s first five Word documents (and an additional document used as a template) can be matched with source documents that were included as attachments to Podesta’s emails. We do not conclude that Podesta’s emails were the actual source of Guccifer 2’s first five Word documents, but note that this conclusion cannot be ruled out.
[2018-02-16] David J. Blake (@HisBlakeness) published his research [archive] that suggests that Guccifer 2’s first two documents were created with GMT+3 time zone offset settings in force.
********************************************************************
BSavant note: I've excluded most of the 'Analysis' section in the interest of space; full content can be viewed at the source link above
********************************************************************
Based on the original change log timestamp, which is 7 hours earlier than the document’s (GMT based) last modified time, we reach the following surprising conclusion.
Guccifer 2’s document, named hillary-for-america-fundraising-guidelines-from-agent-letter.docx, was saved on a computer which had Pacific Daylight Time (PDT) settings in force.
The PDT Finding Invalidates the Prior GMT+3 Findings
In the first part of this report, we documented our analysis, which provided support for the conclusion that Guccifer 2 may have been operating out of a GMT+3 time zone region. However, when we place that conclusion against our finding that a document uploaded by Guccifer 2 (in a similar time frame) was likely last saved in a location on the West Coast, US we have to question our GMT+3 findings.
We must now give serious consideration to the idea that all 25 documents (uploaded in three batches over the course of a month) were all generated on the West Coast, US. Guccifer 2 was possibly working on a VM and/or using a VPN that vectored through Romania or Russia. Here is how that shift will look if all 25 files were last saved on the West Coast (PDT):
For those who might suggest that Guccifer 2 intentionally planted his “West Coast fingerprint”, we ask: what was his motive? His first five documents appear to have been carefully crafted to send the message that they were generated somewhere in Russia, and his working hours appear to be consistent with that conclusion. Why would Guccifer 2 want to undo his hard work?
Comments found within prior related postings on Forensicator's blog:
(bolded portions added)
AY
May 6, 2018 at 6:40 pm
We now have evidence to suggest:
1) Guccifer 2.0 was operating in an American time zone.
2) Guccifer 2.0 documents were obtained from a leak rather than a hack.
3) Many of the “clues” that indicated Guccifer 2.0 was a Russian hacker were carefully constructed.
It’s no longer a stretch to conclude that Guccifer 2.0 was an operation designed to implicate Wikileaks as a Russian stooge and (likely) to take attention away from the content of the released emails. The question, then, remains as to who conducted this operation.
theforensicator
May 6, 2018 at 6:51 pm
From the recent HPSCI report (p 36): “attribution is a bear”. Followed by one full page of redacted text.
Lo Ryder
May 2, 2018 at 7:52 am
Just to be clear, are you suggesting that G2 intentionally implanted a” Russian fingerprint” into 1.doc in order for the the DNC to be able to claim Russia hacked the emails?
I read the whole thing waiting to get the gist of what all that implies. Maybe I need more coffee but I remain uncertain as to what this is ultimately suggesting.
theforensicator
May 2, 2018 at 8:26 am
Are you suggesting that G2 intentionally implanted a” Russian fingerprint” into 1.doc in order for the the DNC to be able to claim Russia hacked the emails?
We do not know who G2 is, nor his intent. The prevailing narrative has been that G2 left behind the “Russian fingerprints” because he was careless and in a hurry to respond to the DNC’s announcement the previous day. No one took a look at what it takes to create those Russian fingerprints (Cyrillic error messages). This report/analysis does that. It is a very long chain of unconventional actions. The reader will have to decide whether G2 was in a hurry/not and whether he was deliberate in constructing those Russian fingerprints/not.
FTM
April 30, 2018 at 6:46 pm
Feel free to “fail” me if I am off base but “Guccifer 2” had Democratic party documents before Wikileaks released these as attachments to the “Podesta” Wikileaks email release?
Does this mean G2 is likely the hacker of Podesta’s emails? Or a party insider with access to the same docs Podesta would likely read?
Did G2 get overly excited about the CS-DNC “hack” announcement and assumed it was about his or her doings with Podesta? Is that why G2 rushed the June 15 modifications? Is that why G2 could not prove their hacking skills–they did not go beyond security password guessing or phishing? Were the Russian Fingerprints to hide G2’s origin…or just playfully malicious?
theforensicator
May 1, 2018 at 6:31 am
“Guccifer 2” had Democratic party documents before Wikileaks released these as attachments to the “Podesta” Wikileaks email release?
Per media reports, the first DNC emails were disclosed by WL on July 22, 2016. Therefore, we could only say with some certainty that G2 may have had access to DNC documents prior to their release only if the documents were released on G2’s web site or to third parties (who made them public) before then.
There were three batches of G2 documents before 7/22: 6/15, 6/18, and 7/6. The 7/6 batch had 9 documents, all can be traced to DNC email attachments. No other batches (before/after 7/22) can be traced to the DNC emails. Note: matching documents by name is an approximate process and not all of G2’s documents could be traced to a source (Podesta emails, DNC emails, ngpvan.7z, cf.7z). G2 modified the metadata on most of the docs in those first 3 drops, mentioned above – therefore exact match is impossible.
Does this mean G2 is likely the hacker of Podesta’s emails? Or a party insider with access to the same docs Podesta would likely read?
We don’t have the info to make that determination. Possession of documents that can be traced to the Podesta emails, doesn’t confirm that those emails were the actual source. Even if we could determine that the Podesta emails are the actual source, we have no way (using public sources) of linking G2 as the perp who took them.
Did G2 get overly excited about the CS-DNC “hack” announcement and assumed it was about his or her doings with Podesta? Is that why G2 rushed the June 15 modifications? Is that why G2 could not prove their hacking skills–they did not go beyond security password guessing or phishing? Were the Russian Fingerprints to hide G2’s origin…or just playfully malicious?
With only G2’s boasting and his document dumps to go on, we have no proof that he did any hacking, much less do we know how the hacking was done.
Why do you say “G2 *rushed* the June 15 modifications”? In our article, we show that the path to disclosing “Russian fingerprints” looks to be long, complex, and deliberate. Putting aside motivation/intent, just walking through those steps would take significant time. On G2’s first day, he had to doctor up 5 Word documents, 5 spreadsheets, communicate with two media outlets (TSG and Gawker), *and* create a blog site. G2 may have been in a hurry, but overall he seems quite organized and deliberate.
There is an alternative scenario, where G2 contacted the media outlets prior to the DNC going public. The media outlets may have tipped off the DNC and then delayed release of their articles until after the DNC got their announcement out via WaPo and Crowdstrike. It may have been the DNC that was playing defense. We just don’t know.
EDIT: This Nov, 2017 article quotes the TSG editor, saying he was contacted by G2 at around noon, the day after the DNC announced it had been hacked. The DNC announcement (WaPo) sourced the Trump opposition report to the DNC hack, not the Podesta emails.
https://www.apnews.com/dea73efc01594839 ... -Democrats
Were the Russian Fingerprints to hide G2’s origin…or just playfully malicious?
That’s the million $BTC question.